DeFi Exploits 2025: A Record-Breaking Year of Sophisticated Attacks and Hard-Won Lessons
From rounding errors to private key compromises, the 2025 DeFi landscape delivered a masterclass in what can go wrong—and what the industry must do differently.
Executive Summary
2025 will be remembered as one of the most consequential years for DeFi security—and not for the right reasons. Despite significant improvements in smart contract auditing and protocol design, total cryptocurrency theft reached approximately $3.4 billion, with the DeFi sector bearing a substantial portion of these losses. The year kicked off ominously when Moby Trade, an options platform on Arbitrum, lost $2.5 million in January's first major hack. It ended with security researchers still cataloging the aftermath of breaches that collectively drained billions from protocols, exchanges, and individual wallets.
But this isn't simply a story of failure. 2025 also demonstrated the growing sophistication of the white hat community, the emergence of protocol-level security improvements, and a fundamental shift in how the industry thinks about attack surfaces. The question facing DeFi participants isn't whether protocols will be attacked, but whether they're prepared when it happens.
This comprehensive analysis examines the major exploits of 2025, dissects the technical vulnerabilities that made them possible, and provides actionable guidance for both users and developers navigating this treacherous landscape.
The Numbers: A Sobering Reality Check
Total Losses by the Numbers
According to Chainalysis data released in January 2026, cryptocurrency theft reached $3.4 billion in 2025—a slight increase from 2024's $3.38 billion. However, the concentration of these losses tells a more complex story:
- Three incidents accounted for 69% of all losses from services
- The Bybit exchange hack alone ($1.4 billion) represented 44% of annual losses
- 158,000 individual wallet compromises affected 80,000 unique victims
- Q1 2025 set an all-time record with $1.64 billion in losses
The Quarterly Pattern
The year followed a distinctive rhythm that security researchers found instructive:
| Quarter | Losses | Notable Trend |
|---|---|---|
| Q1 2025 | $1.64B | Worst quarter on record |
| Q2 2025 | $801M | 52% decrease, shift to mid-sized exploits |
| Q3 2025 | $509M | Code-driven losses dropped sharply |
| September | Spike | 16 million-dollar hacks in single month |
This pattern suggests that while industry-wide security improvements helped reduce the steady drumbeat of smaller exploits, the potential for catastrophic failures remained ever-present.
Case Study #1: Moby Trade — Private Keys and the January Wake-Up Call
What Happened
On January 8, 2025, hackers drained $2.5 million from Moby Trade, a decentralized options platform on Arbitrum, marking the first significant DeFi hack of the year. The attack targeted the protocol's vault contracts, stealing USDC, WETH, and WBTC through what investigators later confirmed was a private key compromise.
The Attack Vector
The attackers gained control of proxy admin keys, which gave them the ability to:
- Upgrade the vault smart contracts
- Insert malicious code granting unauthorized access
- Call the
emergencyWithdrawERC20function to drain assets
The root cause—leaked or stolen private keys—would become a recurring theme throughout 2025.
The Whitehat Rescue
In an unusual twist, MEV researcher Tony Ke from Solayer Labs/Fuzzland identified that the attacker's own smart contract contained an unprotected upgrade function. Using this vulnerability against the attacker, Ke managed to rescue $1.5 million in USDC, returning it to the protocol and reducing total losses by 60%.
The remaining $1 million (207 WETH and 3.7 WBTC) was lost. According to Ke, his counter-hack was only "30 seconds too late" to save those funds as well.
Lessons Learned
The Moby Trade hack illustrated two critical lessons:
For protocols:
- Private key security remains the Achilles' heel of DeFi
- Emergency withdrawal functions need additional safeguards beyond key access
- Even attackers can be attacked if they deploy sloppy code
For users:
- Protocol claims of "audited" status don't protect against operational security failures
- First-mover disadvantage is real—being an early liquidity provider carries outsized risks
Case Study #2: The Cetus Protocol Catastrophe — $223 Million in 15 Minutes
What Happened
On May 22, 2025, Cetus Protocol—the largest DEX on the Sui blockchain—suffered a devastating exploit that drained approximately $223 million in under 15 minutes. The attack exploited a mathematical error in the protocol's liquidity calculations, specifically a flawed integer overflow check.
The Technical Details
The vulnerability resided in the checked_shlw function, designed to prevent integer overflows during bit shift operations. The critical error:
Intended check: value < 0x1 << 192
Actual check: value < 0xFFFFFFFFFFFFFFFF << 192
This seemingly minor difference—comparing against a much larger threshold—allowed certain values that would cause overflows to pass the safety check.
The attacker's methodology:
- Initiated a flash loan for capital
- Created a liquidity position with an extremely narrow tick range [300000, 300200]
- Supplied a liquidity value that passed the flawed overflow check but would overflow during calculations
- Exploited the overflow to manipulate how many tokens were required to claim liquidity—reducing it to just 1 token
- Deposited the single token and received massive liquidity rights
- Extracted this liquidity across multiple transactions
The Recovery
The Cetus team and Sui Foundation coordinated a remarkable recovery effort:
- $162 million remained on the Sui blockchain and was partially recovered
- $60 million was quickly bridged to Ethereum by the attacker
- Affected liquidity pools were eventually restored to approximately 85% of their initial value through treasury funds and a Sui Foundation loan
What This Attack Revealed
The Cetus hack exposed a dangerous assumption in Move programming: that the language's built-in overflow protection makes mathematical exploits impossible. However, bit shift operations intentionally permit overflows, and the Cetus auditors—despite conducting multiple audits—failed to catch the flawed check.
This incident highlighted that:
- Language-level protections aren't comprehensive—developers must understand the exceptions
- Multiple audits don't guarantee security—especially when auditors share the same blind spots
- Recovery is possible—but requires coordination, treasury reserves, and community support
Case Study #3: The Bunni Rounding Error — When Decimals Become Deadly
What Happened
In September 2025, Bunni—an ambitious DEX built on Uniswap v4 hooks—lost $8.4 million to attackers who exploited a rounding error in the protocol's withdrawal function. The attack forced Bunni to permanently shut down operations, marking the end of one of DeFi's most technically complex projects.
The Attack Vector
The vulnerability centered on the withdrawal logic within BunniHubLogic::withdraw(). The critical calculation:
balance.mulDiv(shares, currentTotalSupply)
Was intended to round down when calculating idle balances, but implementation errors caused it to round up instead.
The attacker's exploitation sequence:
- Borrowed funds via flash loan
- Executed precise swaps to manipulate pool price dynamics
- Performed 44 tiny withdrawals that exploited the precision error
- Reduced the pool's active USDC from 28 wei to 4 wei (85.7% reduction)—while only burning 84.4% of liquidity
- Executed sandwich attacks at inflated prices to extract value
The Broader Implications
The Bunni hack carried special significance because it targeted Uniswap v4's hook system—a feature that lets protocols "bolt on" custom liquidity management logic. The incident proved that this flexibility comes with proportional risk:
- Hooks expand the attack surface—custom logic means custom vulnerabilities
- Traditional auditing struggles with novel architectures—the delta handling complexity in Bunni's liquidity distribution logic proved too subtle for standard review
- Precision errors scale catastrophically—what looks like a rounding difference of a few wei can drain millions when amplified through repeated operations
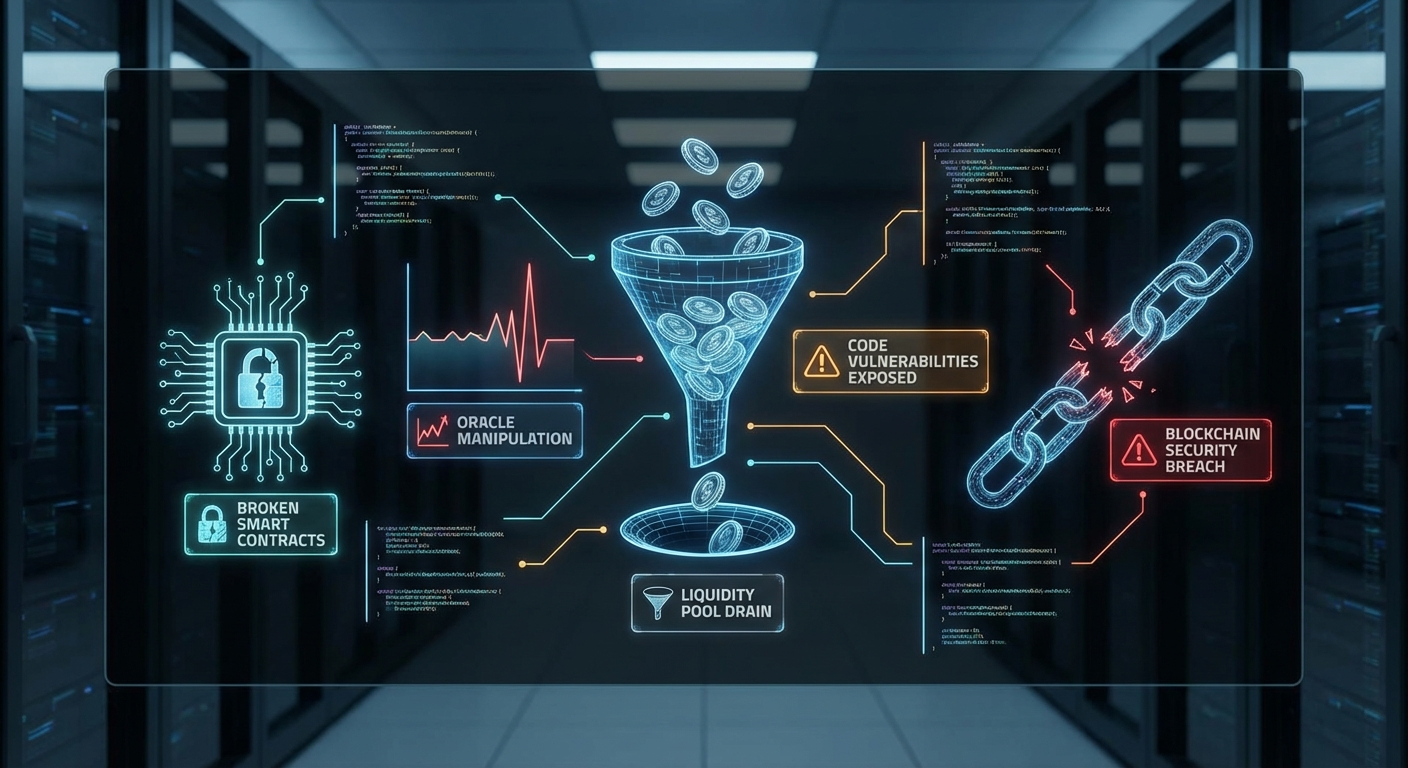
The Pattern: Oracle Manipulation Attacks in 2025
While private key compromises dominated headlines, oracle manipulation attacks surged 31% year-over-year according to CoinLaw research. These attacks share a common pattern:
How Oracle Manipulation Works
- Identify vulnerable price feed — Target protocols that derive prices from single DEX pools or use stale data
- Accumulate capital — Usually via flash loans, eliminating capital requirements
- Manipulate the reference price — Large trades move the pool price that the oracle reports
- Exploit the mispriced asset — Borrow against inflated collateral, liquidate positions at artificial prices, or perform arbitrage
- Repay and extract profit — Complete the flash loan and keep the difference
Notable 2025 Examples
- New Gold Protocol (September): $2 million loss due to price oracle issues combined with transfer logic flaws
- Multiple vault exploits (March): $700K loss when flash loans manipulated exchange rates to mislead price oracles
- Shibarium Bridge (September): Flash loan attack to gain validator signing keys through oracle-adjacent manipulation
Defensive Measures That Work
Protocols that survived 2025 without oracle manipulation incidents typically implemented:
- Time-weighted average prices (TWAPs) instead of spot prices
- Multiple oracle sources with outlier detection
- Freshness checks rejecting stale price data
- Bounds checking on price movements between blocks
- Circuit breakers that pause operations during extreme volatility
The Elephant in the Room: Private Key Compromises
The Dominant Attack Vector
According to CertiK's H1 2025 analysis, wallet compromises accounted for 69% of value lost ($1.71 billion across 34 incidents). This represents a fundamental shift in the DeFi threat landscape:
- Smart contract vulnerabilities are becoming harder to exploit as auditing matures
- Private key compromises offer direct access without needing to understand complex protocol logic
- Social engineering and supply chain attacks target the humans behind the keys
Major 2025 Private Key Incidents
| Protocol | Loss | Attack Method |
|---|---|---|
| Bybit | $1.4B | Supply chain attack on signing infrastructure |
| UPCX | $70M | Malicious smart contract update via compromised key |
| Phemex | $73M | Hot wallet compromise across 16 blockchains |
| Nobitex | $90M | Politically-motivated key theft |
| SwissBorg | $41.5M | Supply chain attack via staking partner |
| Seedify | $1.7M | Developer key compromise (DPRK-attributed) |
Why Keys Keep Getting Compromised
The Bybit attack—the largest in cryptocurrency history—revealed how sophisticated attackers have become at targeting off-chain infrastructure:
- Supply chain infiltration: Attackers compromised Bybit's signing infrastructure, not the smart contracts themselves
- Social engineering: Legitimate-appearing requests tricked signers into authorizing malicious transactions
- Operational complexity: Multi-chain operations create multiple points of failure
How Did Audit Firms Perform in 2025?
The Uncomfortable Truth
A 2026 analysis by SoluLab found that only 20% of hacked protocols had undergone security audits. This statistic, while initially encouraging for audit advocates, reveals a troubling nuance: the 20% that were audited still got hacked.
Where Audits Fell Short
The Cetus case is instructive. Despite multiple audits from reputable firms, the flawed overflow check in checked_shlw went undetected. Contributing factors:
- Language assumptions: Auditors may have assumed Move's overflow protection was comprehensive
- Test coverage gaps: The specific edge case that caused overflow wasn't in test suites
- Audit scope limitations: Code reviews don't always catch logical errors in mathematical functions
The Bunni case demonstrated another limitation: traditional auditing struggles with novel architectures. The precision error in withdrawal calculations represented "precisely the kind of subtle mathematical mistake that becomes catastrophic at scale"—but it required deep understanding of Uniswap v4's hook system to catch.
What Audits Can and Cannot Do
Audits CAN:
- Identify known vulnerability patterns
- Verify code matches specifications
- Catch common mistakes (reentrancy, access control gaps)
- Improve overall code quality through review
Audits CANNOT:
- Guarantee security (nothing can)
- Protect against private key compromise
- Catch every edge case in complex mathematical logic
- Prevent supply chain attacks
- Account for economic attacks unique to specific market conditions
The Emerging Solution: Layered Security
Leading protocols in 2025 moved beyond single audits to comprehensive security programs:
- Multiple independent audits (different firms, different perspectives)
- Formal verification for critical mathematical functions
- Bug bounty programs with meaningful rewards
- Runtime monitoring to detect anomalous behavior
- Incident response plans with tested procedures
- Insurance coverage from on-chain insurance protocols
Is DeFi Getting More or Less Secure? The 2024 vs. 2025 Comparison
By the Numbers
| Metric | 2024 | 2025 | Trend |
|---|---|---|---|
| Total Losses | $2.2B | $3.4B | ⬆️ 55% |
| Number of Incidents | 303 | ~200 | ⬇️ 34% |
| Incidents >$50M | 8 | 6 | ⬇️ 25% |
| Smart Contract Exploits | High | Declining | ⬇️ Improving |
| Private Key Compromises | Rising | Dominant | ⬆️ Concerning |
The Paradox: Fewer Attacks, More Losses
The data reveals a troubling trend: DeFi is getting better at preventing small attacks while remaining vulnerable to catastrophic ones. This suggests:
- Basic smart contract security is maturing
- Audit coverage is improving for on-chain code
- Attackers are shifting to off-chain targets (keys, infrastructure, supply chains)
- When big attacks succeed, they're increasingly sophisticated and damaging
The TVL Context
Despite increased Total Value Locked (TVL) in DeFi throughout 2025, hack losses per dollar locked actually decreased compared to 2021-2022. This suggests:
- Security spending is scaling with value at risk
- Mature protocols are genuinely more resilient
- The "security premium" of established protocols is real
The Verdict
DeFi is getting more secure on-chain but more vulnerable off-chain. The industry has invested heavily in smart contract security, and it shows. However, the human and operational elements—key management, supply chain security, access controls—remain dangerously under-addressed.
Lessons for DeFi Users
Before You Deposit
- Research the team — Anonymous teams aren't automatically bad, but they limit accountability
- Check audit reports — Look for multiple audits from reputable firms (Trail of Bits, OpenZeppelin, Halborn, CertiK, etc.)
- Review TVL history — Sudden spikes or drops can indicate manipulation or exodus
- Understand the token economics — Are there unlimited minting capabilities? Who controls them?
- Test with small amounts — Never deposit your first time with significant capital
Ongoing Risk Management
- Never approve unlimited token spending — Set specific limits
- Regularly review and revoke approvals — Use tools like Revoke.cash
- Use hardware wallets for significant holdings
- Spread risk across protocols — Diversification applies to DeFi too
- Set alerts for contract upgrades — Many protocols post announcements before changes
When Things Go Wrong
- Document everything — Transaction hashes, timestamps, wallet addresses
- Report to the protocol — Many have emergency contacts or bug bounty programs
- Check for recovery efforts — Some hacks result in partial user compensation
- Be wary of "recovery scams" — Attackers often target victims with fake recovery offers
Lessons for Protocol Developers
Smart Contract Security
- Assume overflow is possible — Even in "safe" languages, edge cases exist
- Test mathematical functions exhaustively — Especially at boundaries and with extreme values
- Implement rounding consistently — Document whether operations round up or down, and why
- Use established libraries — OpenZeppelin contracts are battle-tested for a reason
- Consider formal verification — For critical functions, mathematical proofs beat testing
Key Management
- Use hardware security modules (HSMs) — Never store keys in software
- Implement multi-signature requirements — No single key should control critical functions
- Geographic distribution — Keys held in different jurisdictions reduce single points of failure
- Regular key rotation — Limit the window of opportunity for compromised keys
- Access logging — Know who accessed what, when
Operational Security
- Vet dependencies thoroughly — Supply chain attacks are rising
- Implement upgrade timelocks — Give users time to exit before changes take effect
- Monitor on-chain activity — Anomaly detection can catch exploits in progress
- Prepare incident response plans — Know who does what before you need it
- Consider circuit breakers — Automatic pauses when metrics exceed thresholds
The Checklist: What to Look for Before Using a New Protocol
Before depositing funds into any DeFi protocol, verify:
Security Fundamentals
- [ ] Multiple security audits from reputable firms (not just one)
- [ ] Bug bounty program with meaningful rewards (>$100K for critical)
- [ ] Security contact clearly published
- [ ] No critical findings unaddressed in audit reports
- [ ] Timelock on upgrades (minimum 24-48 hours)
Transparency & Governance
- [ ] Team identity (or reputation if pseudonymous)
- [ ] Open source code with verified contracts
- [ ] Clear documentation of how the protocol works
- [ ] Decentralized governance or roadmap toward it
- [ ] Treasury visibility — know where funds go
Technical Design
- [ ] Battle-tested dependencies (forked from established protocols = better)
- [ ] Reasonable upgrade mechanisms (not arbitrary admin control)
- [ ] Oracle diversity (multiple sources, TWAP pricing)
- [ ] Withdrawal functionality always accessible
- [ ] Emergency pause functionality with clear triggers
Track Record
- [ ] Time in production (>6 months preferred)
- [ ] TVL history without unexplained fluctuations
- [ ] No prior exploits (or transparent handling if there were)
- [ ] Active development — recent commits, responsive team
- [ ] Community engagement — active Discord/forum with real users
Red Flags to Watch
- ❌ Anonymous team with new protocol and high APY
- ❌ Single audit from unknown firm
- ❌ Unlimited admin permissions
- ❌ Missing or minimal documentation
- ❌ Pressure to deposit quickly ("limited time!")
- ❌ Token economics that require constant new deposits
- ❌ Angry or dismissive responses to security questions
Conclusion: The Road Ahead
2025 proved that DeFi security is neither a solved problem nor an impossible one. The industry demonstrated genuine progress in smart contract security—code-driven losses declined quarter over quarter, and fewer individual exploits succeeded. However, the catastrophic breaches that did occur revealed how attackers adapt, shifting from on-chain vulnerabilities to off-chain weaknesses in key management, supply chains, and operational security.
The $3.4 billion in total losses serves as both a warning and a mandate. For DeFi to achieve its promise of permissionless, trustless finance, it must earn the trust it asks users to suspend. That means:
- For protocols: Investing in comprehensive security programs that go far beyond single audits
- For users: Approaching DeFi with the due diligence the stakes deserve
- For the industry: Sharing lessons from failures as openly as we celebrate successes
The exploits of 2025 were costly. Making them worthwhile requires learning from them. The protocols that thrive in 2026 and beyond will be those that treat security not as a checkbox, but as a continuous practice—one that evolves as fast as the attackers it defends against.
This analysis was prepared for educational purposes. Nothing in this article constitutes financial advice. Always conduct your own research before interacting with any DeFi protocol.