The $1.5 Billion Bybit Breach: Inside the Largest Cryptocurrency Heist in History
How North Korea's Lazarus Group pulled off a surgical supply-chain attack that rewrote the rules of crypto security—and what it means for every exchange and user in the space.
The Day Crypto Got Its Biggest Wake-Up Call
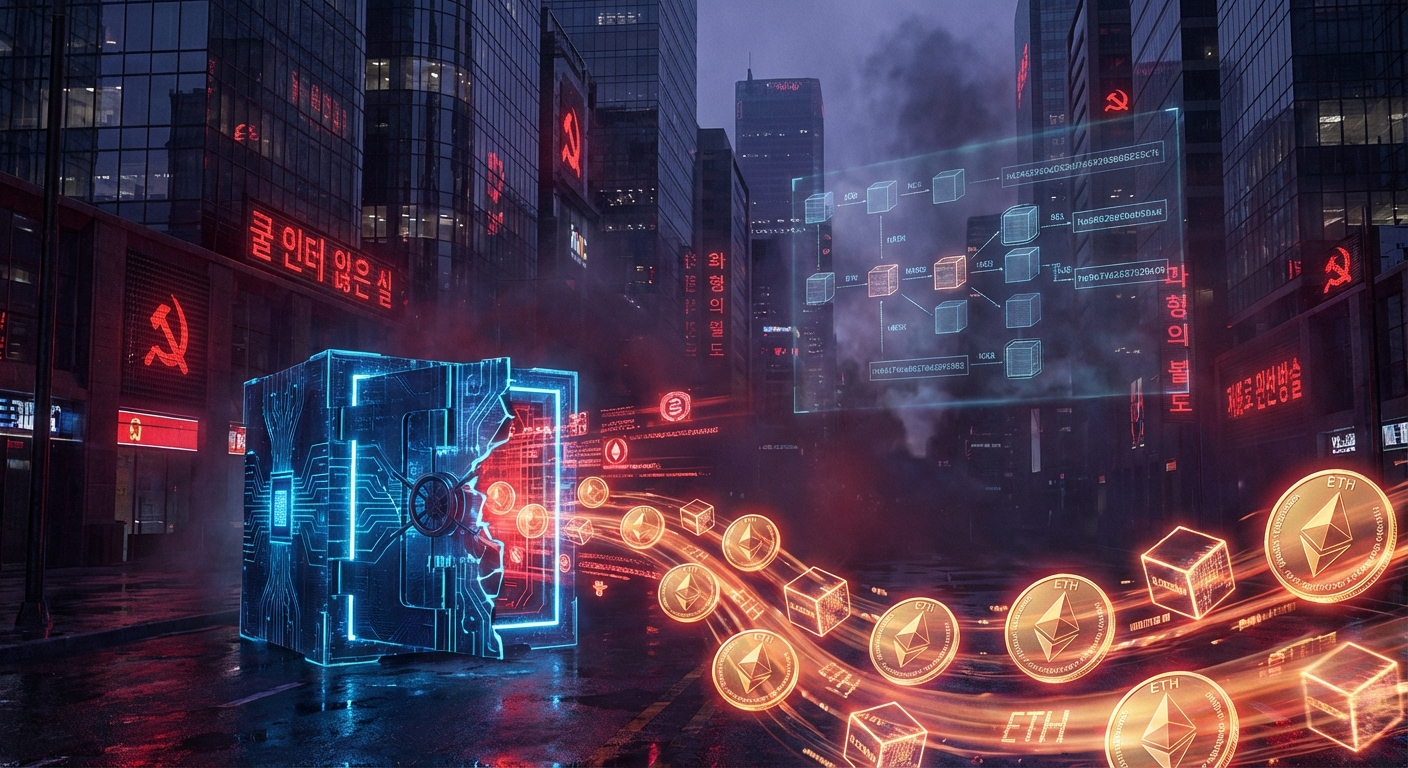
On February 21, 2025, at approximately 2:16 PM UTC, something unprecedented happened in cryptocurrency history. In the span of roughly 30 minutes, 500,000 ETH—worth approximately $1.5 billion—vanished from Bybit's cold storage into a labyrinth of wallets controlled by North Korea's infamous Lazarus Group.
It wasn't just the largest crypto heist ever recorded. If Bybit were a traditional bank, the theft would rank as the largest bank robbery in Guinness World Records history—by a substantial margin. The previous record holder, the 2003 theft of approximately $1 billion from Iraq's Central Bank, suddenly looked quaint by comparison.
But what made the Bybit hack truly terrifying wasn't the amount stolen—it was how it was stolen. This wasn't some script kiddie exploiting a smart contract bug or a hacker brute-forcing private keys. This was a masterclass in patience, precision, and understanding that the weakest link in crypto security isn't code—it's people.
The Anatomy of a Perfect Attack
To understand how the Bybit breach unfolded, you need to forget everything you thought you knew about crypto hacks. This wasn't a technical exploit. It was a supply-chain attack so sophisticated that it would make most nation-state intelligence agencies envious.
Phase 1: The Trojan Horse (February 4, 2025)
The operation began 17 days before the heist itself, when a developer at Safe{Wallet}—the multi-signature wallet platform Bybit trusted to secure its largest holdings—downloaded what appeared to be an innocent Docker project.
The file was titled "MC-Based-Stock-Invest-Simulator-main," and it arrived via what investigators believe was a social engineering attack, likely disguised as a job opportunity or an investment research tool. This kind of approach is Lazarus Group's signature move: blend in, build trust, deliver the payload.
The moment that Docker container ran on the developer's workstation, it established a connection to an attacker-controlled server and began exfiltrating AWS session tokens—the temporary credentials that grant access to Safe{Wallet}'s cloud infrastructure.
With those tokens in hand, the hackers had bypassed multi-factor authentication entirely. They now held the keys to the kingdom.
Phase 2: The Sleeping Dragon (February 4-21, 2025)
Here's where the attack's sophistication truly shines. Most hackers would have moved immediately, grabbing whatever they could before detection. The Lazarus Group did the opposite.
For over two weeks, they waited. During this time, they injected subtle JavaScript code into Safe{Wallet}'s web interface—code specifically designed to remain dormant until it detected that a Bybit employee had opened their Safe account and was about to authorize a transaction.
The brilliance of this approach cannot be overstated. The entire Safe{Wallet} application functioned normally for every other user. There were no outages, no suspicious behavior, nothing that would trigger an audit. The malicious code was a surgical instrument aimed at one target and one target only: Bybit.
Phase 3: The Heist (February 21, 2025)
On that Friday afternoon, Bybit employees initiated what should have been a routine transfer from the exchange's cold wallet to a warm wallet for active trading. Standard operating procedure. Nothing out of the ordinary.
Multiple authorized personnel logged into Safe{Wallet} to approve the transaction—exactly as the multisig security model required. The interface displayed what appeared to be the correct destination address. The amounts looked right. Everything checked out.
What the signers couldn't see was that the malicious code had already swapped in a different command. They weren't approving a routine internal transfer. They were approving a complete drain of Bybit's cold storage.
The exploit leveraged Ethereum's delegatecall function, which allows a smart contract to execute another contract's code within its own storage context. By tricking the signers into changing their wallet's contract logic to a malicious version, the attackers gained full control of the funds.
Within minutes, 500,000 ETH flowed to addresses controlled by North Korea.
Meet the Lazarus Group: The World's Most Profitable Hackers
Within 24 hours of the attack, blockchain investigator ZachXBT had submitted definitive evidence to Arkham Intelligence connecting the hack to North Korea's Lazarus Group. The FBI confirmed this attribution on February 26, 2025, identifying the attackers as "TraderTraitor actors"—one of the known aliases for the DPRK's elite hacking unit.
Lazarus Group isn't your typical cybercriminal organization. It operates under North Korea's Reconnaissance General Bureau and serves a single purpose: funding the regime's nuclear weapons and ballistic missile programs. The stolen cryptocurrency doesn't go to fancy cars and expensive watches. It goes to centrifuges and warheads.
The numbers paint a chilling picture:
- 2025 total: North Korean hackers stole $2.02 billion in cryptocurrency
- Bybit's share: $1.5 billion—or 74% of their entire 2025 haul from a single attack
- Since 2017: Over $6.75 billion in documented crypto theft
- Year-over-year growth: 51% increase from 2024 to 2025
- Global share: North Korea accounted for 59% of all cryptocurrency stolen worldwide in 2025
The Bybit hack alone represented one-third of all crypto stolen globally in 2025 ($3.4 billion total). No other threat actor—whether nation-state or criminal—comes remotely close to this scale.
The Geopolitical Shadow War
What makes the Bybit breach particularly sobering is understanding its context within North Korea's broader strategy. The regime has effectively industrialized cryptocurrency theft as a primary revenue stream, circumventing international sanctions that have crippled its traditional economy.
According to analysts, cryptocurrency theft now funds a significant portion of North Korea's weapons development programs. The February 2025 BBC investigation into the Bybit hack drew explicit connections between the stolen funds and the country's expanding nuclear and ballistic missile capabilities.
This isn't just cybercrime—it's economic warfare conducted through keyboards rather than battlefields. And unlike traditional state espionage, there's virtually no deterrent. North Korea already faces the strictest sanctions possible; they have nothing to lose.
The Chinese Laundromat
Stealing $1.5 billion in crypto is only half the challenge. Converting it to usable funds is equally complex—especially when every blockchain analytics firm on the planet is watching.
Rather than cash out directly, North Korea has outsourced money laundering to what investigators call the "Chinese Laundromat"—a sprawling network of underground bankers, OTC brokers, and trade-based laundering intermediaries operating primarily in Southeast Asia.
By March 20, 2025—less than a month after the heist—Bybit CEO Ben Zhou reported that hackers had already converted 86.29% of the stolen ETH to Bitcoin through a dizzying array of intermediary wallets, decentralized exchanges, and cross-chain bridges.
The 45-day laundering cycle following major thefts has become a predictable pattern. Zhou noted that 88.87% of stolen assets remained "traceable"—but "traceable" doesn't mean "recoverable" when funds flow through jurisdictions with zero cooperation with international law enforcement.
Bybit's Response: A Masterclass in Crisis Management
If the Lazarus Group demonstrated the highest level of attack sophistication, Bybit's response set a new standard for exchange crisis management.
Within 30 minutes of discovering the breach, CEO Ben Zhou appeared on X (formerly Twitter) with a message that would define the exchange's survival strategy: "Bybit is Solvent even if this hack loss is not recovered, all of clients assets are 1 to 1 backed, we can cover the loss."
It was bold, direct, and exactly what panicking users needed to hear.
The 72-Hour Sprint
Over the next three days, Bybit executed what can only be described as a financial emergency response:
- 350,000+ withdrawal requests processed within the first 12 hours—demonstrating that despite the catastrophic loss, operations continued normally
- 447,000 ETH secured through emergency funding from partners including Galaxy Digital, FalconX, and Wintermute
- 40,000 ETH loan from competing exchange Bitget—repaid within three days
- Proof-of-reserves audit by cybersecurity firm Hacken confirming 100%+ collateralization of major assets
The transparency was unprecedented. Zhou's real-time updates on social media kept the community informed at every step, preventing the kind of speculation and bank-run panic that has destroyed exchanges in the past.
War Against Lazarus
Zhou didn't just play defense. He declared "war against Lazarus" and launched a global bounty program offering up to 10% of recovered funds as rewards for information leading to frozen assets.
By year's end, Bybit had paid $2.18 million in USDT to contributors who helped trace or recover funds. While the total recovery remained minimal—approximately $50 million frozen—the bounty program demonstrated a new model for industry-wide collaboration against state-sponsored threats.
The Market's Verdict
Despite losing $1.5 billion, Bybit not only survived—it thrived. By the end of 2025, the exchange had:
- Crossed 80 million users globally
- Recorded $7.1 billion in daily trading volume
- Ranked 5th among cryptocurrency spot exchanges
- Secured the UAE's first full Virtual Asset Platform Operator License
The crisis response had become a case study in how to survive a catastrophic hack through transparency, preparation, and community trust.
The Broader 2025 Hack Landscape
The Bybit breach dominated headlines, but it was part of a disturbing trend. Total cryptocurrency theft reached $3.4 billion in 2025—a new record and the third consecutive year of increases:
- 2023: $2 billion stolen
- 2024: $2.2 billion stolen
- 2025: $3.4 billion stolen
Perhaps most concerning is the shift in attack vectors. According to Immunefi's 2025 analysis, the majority of major hacks were perpetrated through social engineering rather than technical vulnerabilities.
"Onchain security is improving," noted Immunefi's CEO. "But human error and AI-enabled scams are taking center stage."
Hackers are no longer primarily hunting for smart contract bugs or cryptographic weaknesses. They're targeting people—developers, executives, signers, and anyone with elevated access to critical systems.
Security Lessons for Exchanges
The Bybit hack exposed fundamental vulnerabilities in how even the largest exchanges approach security. Here are the critical lessons:
1. Third-Party Risk Is Existential
Bybit didn't have a security failure. Safe{Wallet} did. But Bybit suffered the consequences.
The crypto industry has built complex dependency chains where exchanges rely on wallet providers, wallet providers rely on cloud infrastructure, and cloud infrastructure relies on individual developer workstations. A compromise anywhere in this chain can cascade catastrophically.
Action: Conduct rigorous third-party security audits. Require vendors to meet the same security standards you apply internally. Consider the entire supply chain as part of your attack surface.
2. Cold Storage Isn't a Magic Shield
The industry has long treated cold wallets as the gold standard of security. But Bybit's funds were in cold storage when they were stolen.
The vulnerability wasn't in storage—it was in the process of moving funds. When transfers become routine, signers develop a false sense of security, treating approvals as formalities rather than critical security decisions.
Action: Implement mandatory delays for large withdrawals. Require additional verification steps for transfers exceeding defined thresholds. Never let security become a rubber-stamp process.
3. The UI Is a Single Point of Failure
Multisig security assumes that signers can verify what they're approving. But if the interface displaying transaction details is compromised, verification becomes meaningless.
The Bybit attackers showed signers one thing while executing another. No amount of cryptographic security could prevent approval of a transaction that appeared legitimate.
Action: Implement pre-signing transaction simulations that show the actual destination and outcome of a transaction before approval. Consider hardware wallet displays as the source of truth rather than web interfaces.
4. Migrate from Multisig to MPC
Following the Bybit hack, most top-tier exchanges have migrated from traditional smart-contract multisigs to Multi-Party Computation (MPC) technology.
Unlike Safe{Wallet}'s setup, MPC splits private keys into shards that never exist in a single location, making UI-spoofing and "ice phishing" attacks nearly impossible to execute.
Action: Evaluate MPC custody solutions for critical assets. The technology has matured significantly and now represents the industry standard for institutional security.
Security Lessons for Individual Users
You might think the Bybit hack is an "exchange problem" that doesn't affect you. That would be dangerously wrong.
1. Not Your Keys, Not Your Crypto (Still True)
Every centralized exchange—no matter how large, well-funded, or transparent—carries custodial risk. Bybit's response was exemplary, but most exchanges couldn't survive a $1.5 billion hit.
Action: Keep only trading funds on exchanges. Long-term holdings belong in hardware wallets under your direct control.
2. Verify Everything, Trust Nothing
The Bybit hack succeeded because trusted employees approved a malicious transaction that appeared legitimate. As a user, you face similar risks every time you connect a wallet to a dApp or approve a transaction.
Action: Before approving any transaction, verify the destination address independently. Use transaction simulation tools. Never rush through approval prompts.
3. Beware Social Engineering
The attack chain began with a developer downloading a fake stock trading simulator—likely delivered through a targeted job offer or investment opportunity.
You face similar risks constantly: fake customer support, phishing links, malicious browser extensions, and increasingly sophisticated scams that use AI-generated content.
Action: Assume all unsolicited contacts are potentially malicious. Never download software from unverified sources. Use dedicated devices for high-value crypto operations.
4. Diversify Across Custody Solutions
No single security measure is foolproof. The Bybit hack demonstrated that even industry-standard practices can be defeated by sufficiently motivated attackers.
Action: Distribute assets across multiple custody solutions: hardware wallets from different manufacturers, different exchanges for trading, and consider multi-signature setups for larger holdings.
Regulatory Implications: The Compliance Tsunami
The Bybit breach is already reshaping the regulatory landscape worldwide.
European Union: MiCA Stage 2
In the wake of the hack, the EU accelerated "Stage 2" of the Markets in Crypto-Assets (MiCA) regulation. New requirements mandate:
- Quarterly audits of third-party software vendors
- Enhanced security certification requirements
- Mandatory incident reporting within 24 hours
United States: Real-Time Proof-of-Reserves
U.S. regulators have intensified focus on mandatory, real-time Proof-of-Reserves (PoR) requirements. The SEC has signaled that custodial exchanges may face enhanced security disclosure requirements.
Global Standards Emerging
Expect industry-wide mandates for:
- Hardware security modules (HSMs) for key management
- Real-time transaction monitoring and anomaly detection
- Enhanced AML frameworks and transaction delays for large transfers
- Regular penetration testing and security certifications
Security and compliance are rapidly becoming threshold requirements for market access. Exchanges that cannot demonstrate robust key management and credible security frameworks will find themselves cut off from banking partners and institutional users.
The Arms Race Continues
North Korea's Lazarus Group has industrialized cryptocurrency theft to a degree that would have seemed impossible a decade ago. They've stolen over $6.75 billion since 2017, with 2025 marking their most successful year yet.
The Bybit hack succeeded not because of some novel zero-day exploit, but because attackers understood a fundamental truth: humans, not code, are the weakest link.
The crypto industry is now in an arms race with state-sponsored hackers who have unlimited patience, sophisticated technical capabilities, and no fear of consequences. Until the industry treats operational security with the same rigor it applies to cryptographic security, these attacks will continue.
The question isn't whether another billion-dollar hack will happen—it's when, and whether the next target will respond as effectively as Bybit did.
Your Actionable Takeaways
For Exchange Operators:
- Conduct immediate security audits of all third-party vendors
- Implement transaction simulation requirements for all large transfers
- Evaluate MPC custody solutions for critical asset storage
- Establish incident response playbooks and test them regularly
- Build relationships with industry partners for emergency liquidity
For Individual Users:
- Move long-term holdings to hardware wallets immediately
- Enable all available security features on exchange accounts
- Use transaction simulation tools before approving any significant transaction
- Maintain healthy skepticism toward unsolicited contacts
- Diversify custody across multiple solutions
For the Industry:
- Share threat intelligence through industry consortiums
- Develop standardized security certification requirements
- Build collaborative incident response capabilities
- Invest in user education about social engineering threats
- Treat the human layer as the primary attack surface
The Bybit hack was a $1.5 billion lesson. The only question now is whether the industry will learn from it—or wait for the next record to be broken.